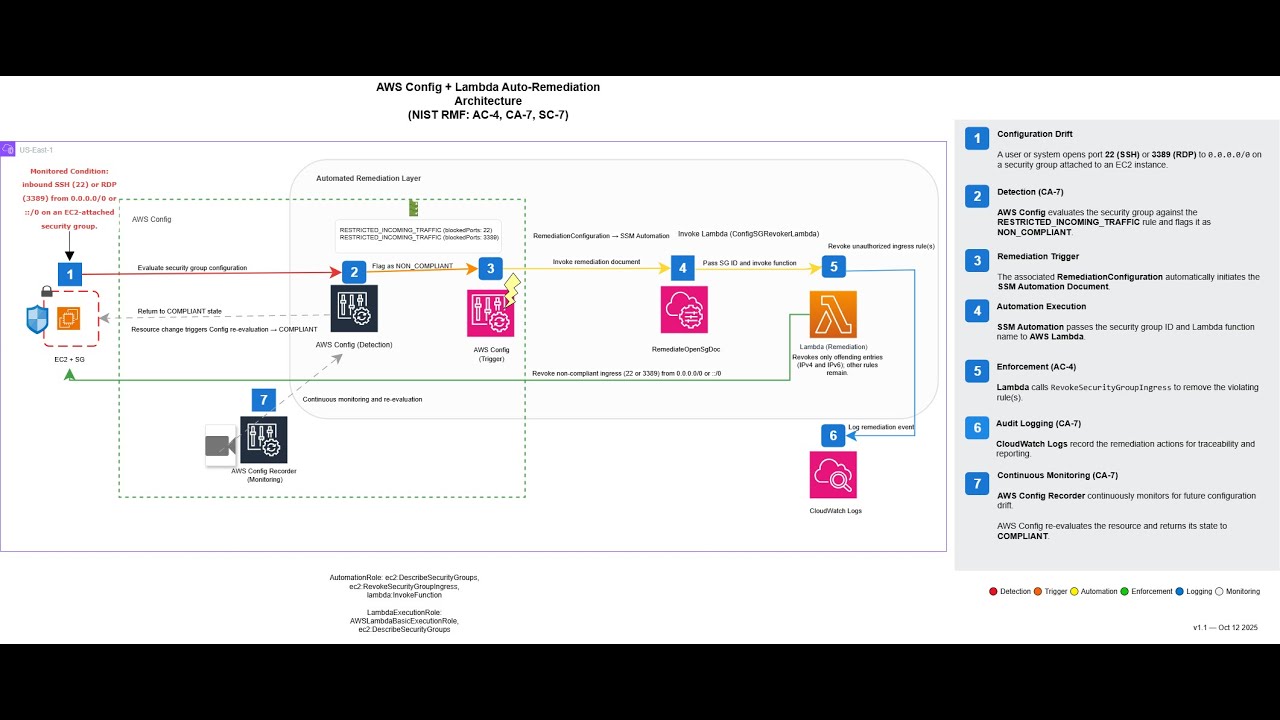
Automated enforcement of NIST RMF controls AC-4, CA-7, and SC-7 through continuous monitoring, automated remediation, and compliance validation of AWS Security Group configurations that expose SSH (22) or RDP (3389) to 0.0.0.0/0.
This project implements an automated security control system that continuously monitors and remediates critical network vulnerabilities in AWS environments. Specifically, it prevents unauthorized exposure of Remote Desktop Protocol (RDP) port 3389 and Secure Shell (SSH) port 22 to the public internet (0.0.0.0/0).
The system continuously monitors Security Groups for configuration drift related to administrative ports (22 and 3389) open to the public internet. When a violation is detected, AWS Config triggers an automated remediation workflow that restores the resource to a compliant state within minutes.
Watch a 7-minute technical demonstration of this project in action:
Click to watch: Problem → Architecture → Live Demo → Results
Publicly accessible administrative ports represent one of the most critical security vulnerabilities in cloud infrastructure. When SSH (port 22) or RDP (port 3389) are exposed to 0.0.0.0/0, you essentially leave the front door to your servers wide open to the entire internet.
Risk Level Summary:
| Component | Port | Protocol | Risk Level | Impact |
|---|---|---|---|---|
| SSH | 22 | TCP | High | Direct command-line access to server |
| RDP | 3389 | TCP | Critical | Full graphical desktop access |
| Source | 0.0.0.0/0 | N/A | Maximum | Any IP address globally can connect |
Automated bots continuously scan the internet for exposed ports 22 and 3389. With world-open access, attackers can launch sustained credential-guessing campaigns:
- SSH: Bots attempt common usernames (
admin,ubuntu,ec2-user) and passwords to gain command-line access - RDP: Attackers target credentials for full interactive desktop sessions, often resulting in immediate system compromise
Public exposure amplifies the impact of service vulnerabilities:
Real-World Example: The 2019 BlueKeep vulnerability (CVE-2019-0708) allowed attackers to achieve remote code execution via RDP without authentication. Publicly exposed port 3389 instances were the primary attack vector for mass exploitation.
Open administrative ports leak valuable intelligence even on fully patched systems, enabling attackers to:
- Identify operating system types and versions
- Build detailed infrastructure profiles
- Plan targeted attacks with precision
This automation implements a structured control flow that aligns with NIST RMF: Drift Detection → Automated Remediation → Audit & Continuous Monitoring
Monitored Condition: Inbound rules allowing SSH (22) or RDP (3389) from 0.0.0.0/0.
Figure: Automated enforcement workflow showing AWS Config detection, Lambda enforcement, and CloudWatch logging.
This solution operates post-deployment as part of a defense-in-depth strategy.
Preventive guardrails in the CI/CD pipeline can block insecure configurations before they are deployed, while this enforcement layer ensures continuous protection in the live environment.
- **AWS Config continuously evaluates Security Groups using the managed rule RESTRICTED_INCOMING_TRAFFIC for ports 22 and 3389.
- **Any violation (such as an SSH or RDP rule open to 0.0.0.0/0) is automatically flagged in near real time.
- **This supports continuous monitoring by detecting configuration drift as soon as it occurs.
- SSM Automation Document orchestrates remediation.
- AWS Lambda revokes only the offending ingress entries (IPv4 and IPv6), preserving legitimate rules.
- **This targeted enforcement supports access control and boundary protection without disrupting approved configurations.
- **CloudTrail records API activity across Config, Lambda, SSM, and EC2.
- **CloudWatch Logs capture Lambda execution, including timestamps and status.
- SSM Automation retains workflow history.
- **AWS Config tracks configuration state changes and compliance history.
- **These logs and records support the AU control family by providing traceable evidence of detection and enforcement events.
- **They also strengthen CA-7 by enabling continuous oversight and reporting.
While this solution focuses on post-deployment detection and automated remediation, it is most effective when paired with preventive controls to minimize risk and exposure windows.
- Pipeline Guardrails: Integrate security checks into the CI/CD pipeline using tools like Checkov, Terraform Cloud Policy Sets, or AWS Service Control Policies (SCPs) to block insecure security group rules before they are deployed.
- Policy Enforcement: Use service control policies or organizational guardrails to ensure only approved configurations are allowed in production.
- Layered Protection: By combining preventive controls with continuous monitoring, even if a rule slips through the pipeline, AWS Config and Lambda remediation will enforce compliance automatically.
This layered strategy aligns with Zero Trust and defense-in-depth principles, reducing both the likelihood and impact of misconfigurations.
| Control | Name | Layer | Implementation |
|---|---|---|---|
| AC-4 | Information Flow Enforcement | Enforcement | Lambda function enforces network access restrictions by revoking unauthorized ingress rules while preserving legitimate access. |
| CA-7 | Continuous Monitoring | Detection & Audit | AWS Config continuously evaluates security groups for drift. Compliance status and resource history support ongoing visibility, while CloudWatch and SSM provide operational awareness. |
| SC-7 | Boundary Protection | Enforcement | Automated enforcement ensures the principle of least privilege at the network perimeter by removing dangerous ingress rules (22/3389 to 0.0.0.0/0). |
| AU-2 | Auditable Events | Audit | Events are generated for security group modifications, remediation actions, compliance state changes, Automation invocations, and Lambda executions. |
| AU-3 | Content of Audit Records | Audit | CloudTrail records API caller identity, event time, source IP, and request details. Lambda logs capture execution results and outcomes. |
| AU-8 | Time Stamps | Audit | CloudTrail and CloudWatch Logs use standardized UTC timestamps to ensure consistent time correlation. |
| AU-12 | Audit Generation | Audit | CloudTrail and CloudWatch generate and store detailed audit records of detection, remediation, and compliance actions. |
Audit hardening (optional): Enable CloudTrail log file integrity validation, encrypt the trail bucket with SSE-KMS, configure retention policies, and add delivery/remediation alarms for better operational visibility.
Assumption: An account or organization CloudTrail trail is enabled and delivering to S3.
This automation targets Security Group ingress rules that:
- Allow SSH (22) or RDP (3389)
- Have a source of 0.0.0.0/0
- Are attached to EC2 instances in scope
Violations trigger AWS Config RemediationConfiguration → SSM Automation → Lambda.
- AWS CLI configured with appropriate credentials
- IAM permissions for CloudFormation, Config, Lambda, SSM, and EC2
git clone https://github.com/Nisha318/config-auto-revoke-sg.git
cd config-auto-revoke-sg
aws cloudformation deploy \
--template-file cloudformation/remediation-stack.yaml \
--stack-name RMF-Auto-SG-Remediation \
--capabilities CAPABILITY_NAMED_IAM
Test in a non-production account. Opening 22/3389 to 0.0.0.0/0, even briefly, can expose instances to scanning.
CloudFormation Stack Deployed:

AWS Config Dashboard (All Compliant):

Initial Security Group States (No Inbound Rules):
Simulated Attack: Opening Ports to 0.0.0.0/0
Config Rules Triggered (Non-Compliant Status):

Non-Compliant Resource Inventory:
sg-0679685bff76924c8(SSH Security Group)sg-08b6df131d94b0ae4(RDP Security Group)
Lambda Execution Logs (CloudWatch):
Final Security Group State (Rules Revoked):

✅ Result: Unauthorized ingress rules automatically removed, security posture restored
config-auto-revoke-sg/ ├─ cloudformation/remediation-stack.yaml ├─ src/lambda/revoke_sg/app.py # or lambda/revoke_rules_handler.py ├─ assets/images/architecture.png └─ assets/images/... # walkthrough screenshots
Complete infrastructure as code defining Config rules, Lambda function, SSM automation, and IAM roles.
📄 View: cloudformation/remediation-stack.yaml
Python function that identifies and revokes non-compliant security group rules using EC2 API.
📄 View: config-auto-revoke-sg/revoke_rules_handler.py
# Core remediation logic
response = ec2.revoke_security_group_ingress(
GroupId=sg_id,
IpPermissions=[rule]
)
print(f"Revoked {len(ip_permissions)} rule(s) on {sg_id}")
print(f"Response: {response['ResponseMetadata']['HTTPStatusCode']}")Instead of 0.0.0.0/0, restrict SSH and RDP access to:
- Corporate IP Ranges: Specific CIDR blocks (e.g.,
203.0.113.0/24) - Bastion Hosts: Dedicated jump servers with hardened configurations
- VPN Endpoints: IPsec or OpenVPN termination points
- AWS Systems Manager Session Manager: Eliminates need for direct SSH/RDP entirely
This automation enforces the fundamental security principle:
Grant only the minimum network access required for legitimate business operations
- Lambda execution success/failure rates
- Config rule evaluation frequency
- SSM automation execution duration
Consider adding SNS topics for:
- Non-compliance detections
- Remediation execution failures
- Repeated violation patterns (indicating potential attacks)
Watch a 7-minute technical demonstration of this project in action:
Contributions are welcome! Please submit pull requests or open issues for:
- Additional security controls
- Enhanced logging capabilities
- Performance optimizations
- Documentation improvements
MIT License
Copyright (c) 2025 Nisha318
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the "Software"), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
Built on AWS native services following NIST Risk Management Framework (RMF) guidelines and security best practices.
Project Maintainer: Nisha P McDonnell Repository: https://github.com/Nisha318/